I've mentioned DD-WRT firmware in the past - it's an open-source replacement firmware for lots of cheap domestic internet routers. If the stock firmware on your router isn't doing it for you or you just want to see what all the fuss is about it is a superb way to make your £50 beige plastic router really sing; enterprise level network control for not much effort. It can terminate VPNs, do QOS and lots of the things you'd normally expect from a Cisco business class device.
Not all routers can take a different firmware image, but if yours is based on the Broadcom 54G chipset (an awful lot are) then you're away to the races; otherwise it's £15 on eBay!
Now then, my two eldest boys are away to university this month and it turns out that one of them is going to live in a student house that only has WiFi - I intended that they would both take DD-WRT routers with them to isolate their little dorm-room networks from IT ne'er do wells (NAT - Network Address Translation, the kind you get with a router, is an excellent defense against port-scanners). BUT, without a wired connection to place on the WAN side of the router how do you isolate and provide both wired and wireless connections behind the router's firewall? My first thought was to buy one of those "connect your Sky+ box Ethernet to your WiFi" adapters. It would turn the insecure WiFi into a wired connection that would sit on the WAN side of the router.
BUT, it's one more thing to go wrong and I was sure that DD-WRT could do it with a bit of tinkering. I looked at a few of the guides online and they were very convoluted with warnings about obscure settings causing trouble and so I decided to figure it out from scratch. It went surprisingly well and now I have a Linksys router that can attach to an existing WiFi access point and then NAT that connection through to another WiFi segment as well as the wired RJ45 links.
So, couple of things to point out.- My home WiFi's SSID is thorpedale4 and the IP range is 10.100.100.x (.8 is the router)
- I wanted all the hosts on the other side of the Linksys to be on a 192.168.1.x network
First up - I set the Linksys to not be an Access Point but to be a client wireless device (taking baby steps; I just wanted to make sure I could attach it to the house WiFi)
This is done under wireless>basic settings>wireless mode and is set to client and then go to wireless security and make sure you've entered the necessary settings (WPA key etc)
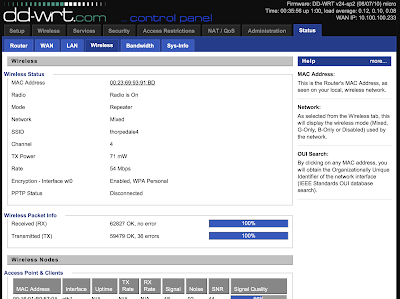
Reboot the router and check it is connecting to the external WiFi - see above. After this make sure you can get out to the internet from a wired connection on the Linksys. At this point the Linksys will be passing back all protocols to the main router and so you'll find the laptop is on the same IP range as the main network and there is no link-isolation (no firewall between the two networks) - we're not there yet!
Next, set the wireless>basic settings>wireless mode to repeater and add in a second virtual wireless interface (this will be your new wireless segment);
Then set up the security - again, the first is for the wireless you're attaching to;
BUT, the second is for the new network you're creating. As the router is now in repeater mode the new wireless segment is on a separate IP subnet (found in the setup>basic settings tab) and by default on the 192.168.1.x segment. The same applies to the wired connections on the Linksys - job done!
Attaching to the new network is as you'd expect;
and looking at the network details shows we're not on the house's 10.100.100.x network;
In fact, trying to reach the new network from the "outer" network;
As far as I can tell there is only one downside to this method - speed; the 54G wireless is now only running around 22Mbits/sec on both segments and that's no surprise as the Linksys is having to hold up two 802.11 links (different frequencies) using only one radio.
BUT, I have a router than can happily attach to a potentially insecure wireless network and produce a new wireless segment as well as wired Ethernet with the SPI (state-full packet inspection) firewall in the way. I paid around a tenner for the router!
BUT, I have a router than can happily attach to a potentially insecure wireless network and produce a new wireless segment as well as wired Ethernet with the SPI (state-full packet inspection) firewall in the way. I paid around a tenner for the router!





No comments:
Post a Comment